LockBit 5.0 in Portugal: The End of the Illusion of Periphery and the Operational Urgency of NIS2

Opinion Piece
Lucas Valente Lima | Offensive SecurityEngineer, Highdome (Agap2IT)
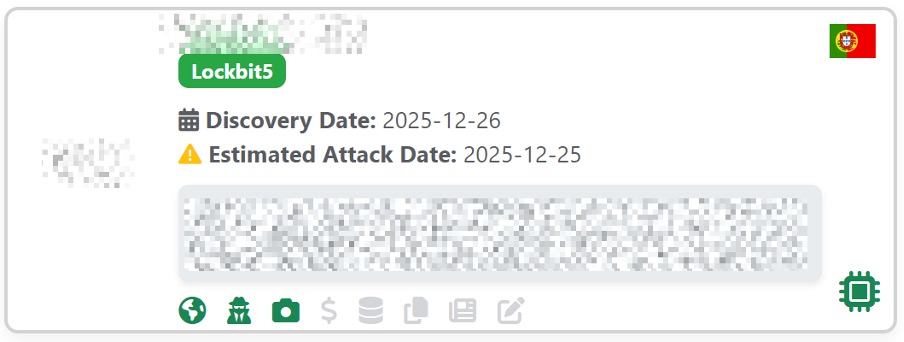
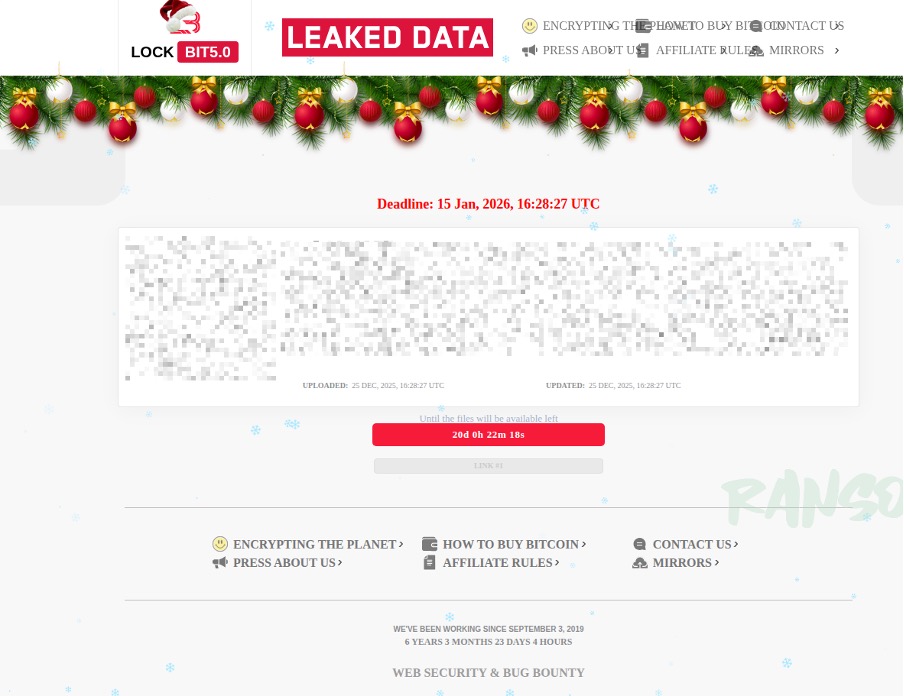
On the night of December 25, 2025, while most of the country was at the table with their families, LockBit 5.0 encrypted the systems of at least two Portuguese organizations. Without warning. Without prior negotiation. With a deadline of January 15, 2026, for the ransom payment, and with data already exposed on the group's leak platform. The timing was not an accident, it was a tactic. And the message was crystal clear: Portugal is not periphery. It is a target.
This is not an academic exercise. It is not a hypothetical scenario in a CNCS report. It is what happened. And what happened compels us to have an uncomfortable conversation about the real state of cybersecurity in Portugal and what NIS2 represents in this context. Not as a regulation. As a survival test.
What LockBit really represents
Talking about LockBit in 2026 requires abandoning the simplistic narrative of a "hacker group." What we have ahead of us is a six-year-old enterprise ransomware-as-a-service operation that survived Operation Cronos in 2024, the largest joint police operation against ransomware of all time, which seized their servers and exfiltrated decryption keys, and came back stronger. How many Portuguese companies could achieve the same after a disruption of this magnitude?
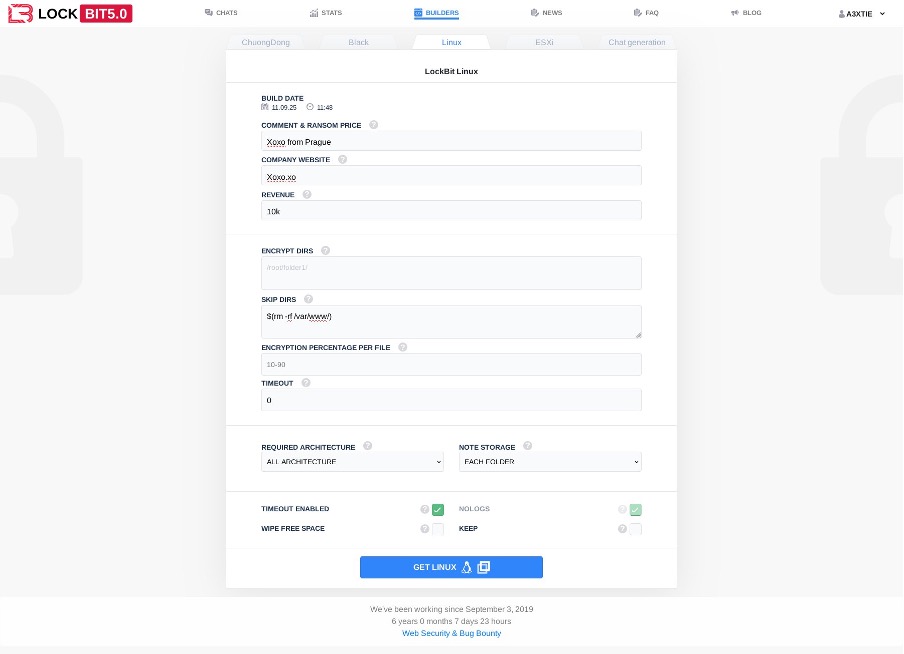
The evolution of LockBit is a case study in continuous innovation. It began in 2019 as the ABCD ransomware, with rudimentary local cipher capabilities. It went through LockBit 2.0 with the introduction of StealBit for automated exfiltration and propagation via SMB. In 3.0, it launched a bug bounty program (yes, a bug bounty program for malware) and implemented intermittent ciphering that drastically accelerated its impact. Version 4.0 brought a complete rewrite to .NET Core, focusing on stealth, API unhooking, and the elimination of noisy features. And now, version 5.0, with its modular architecture, recruits new affiliates with renewed incentives and signals coordination with other groups in an almost cartel-like model.
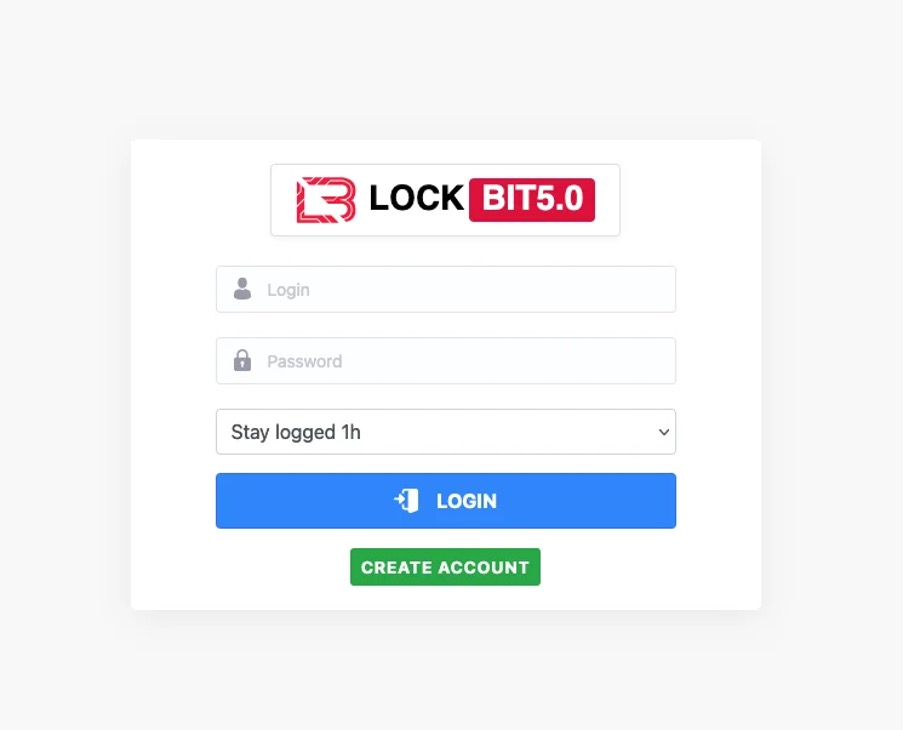
This level of sophistication is not a technical curiosity. It's a strategic problem. We are facing an adversary that operates development cycles, has product management, recruits talent, and has operational resilience. Treating it as "just another ransomware group" is equivalent to ignoring a competitor because "we've seen this before."
Portugal is no longer a periphery.
Let's go back to Christmas 2025. Two Portuguese organizations, with estimated attack dates of December 25th and discovery on the 26th. The data was uploaded to the LockBit 5.0 leaks platform with a payment deadline of January 15th, 2026. The extortion message, the countdown timer, the Christmas branding on the leaks page—everything was calculated to maximize psychological pressure during a period when security teams are reduced to a minimum.
These cases reveal three structural weaknesses that no regulatory framework can solve on its own.
First: monitoring during critical periods. The choice of Christmas Day was not accidental. Ransomware groups know that holidays, public holidays, and weekends are windows of opportunity. How many Portuguese SMEs have continuous 24/7 monitoring? How many even have an incident response plan that works outside of business hours?
Second: speed of response. Between the estimated attack on December 25th and its discovery on the 26th, at least one day passed. In a LockBit 5.0 attack, with optimized intermittent cipher and exfiltration modules, a day is an eternity. The damage is already done before anyone notices.
Third: public exposure. The data was published. The Portuguese flag appears on the LockBit 5.0 leak platform. This is not just a technical problem; it's a reputational, legal, and strategic problem. And this is where the connection with NIS2 becomes inescapable.
NIS2: Regulation or maturity test?
Decree-Law No. 125/2025, which transposes NIS2, comes into force on April 3, 2026. It provides for a 12-month grace period for the application of fines, provided that the entity demonstrates that it has an adaptation procedure underway. Fines can reach 10 million euros or 2% of global turnover. And, critically, the managing bodies become directly responsible, and may be held personally liable for action or omission.
All this sounds good on paper. But let's look at the Natal cases. NIS2 obligations require, among other things: continuous monitoring, tested continuity plans, vulnerability management, multi-factor authentication, encryption of sensitive data, and incident notification within tight deadlines. Now ask yourselves: if these measures had been implemented in the attacked organizations, would the result have been different?
The honest answer is: it depends. And this "it depends" is the crux of the problem. Because NIS2 establishes the minimum. And the minimum isn't enough for LockBit 5.0. LockBit 5.0 kills EDR and antivirus processes, eliminates shadow copies, executes payloads in memory, unhooks APIs to evade detection, and its affiliates use stolen legitimate credentials that pass any previously authenticated MFA. Prevention alone is not enough. And this is where compliance and resilience diverge.
Compliance is having a documented incident response plan. Resilience is that plan working at 11 PM on Christmas Day.
The Hiscox Cyber Preparedness Report 2025 indicates that 54% of Portuguese SMEs have been targeted by cyberattacks. The CNCS reports a significant increase in incidents, with phishing and smishing as the main vectors. These numbers are not abstractions; they are the context in which NIS2 falls. A context in which the overwhelming majority of the Portuguese business fabric is composed of SMEs, many of them without universal MFA, without EDR, without tested offline backups, and without monitoring that works outside of office hours.
And even SMEs that are not directly covered by NIS2 cannot ignore this reality. Why? Because NIS2 demands supply chain security. An SME that is a supplier to an essential or important entity becomes, in practice, a regulated risk vector. If the SME is compromised and the incident affects the client covered by NIS2, there is liability. Period.
The comfortable myths we need to abandon.
I know the counter-arguments. I hear them regularly. Let's dissect the three most common ones.
“Portugal is not a priority target.” I concede that Portugal is not the United States or Germany in terms of sheer volume of attacks. But LockBit's RaaS model doesn't work through centralized geographic prioritization. It works through affiliates. And affiliates attack where they find vulnerabilities. LockBit 5.0 opened up affiliate recruitment with lower barriers to entry and self-registration. More affiliates mean more target diversity. A country with a predominantly SME business fabric, with uneven levels of security maturity, is precisely the kind of terrain that attracts opportunistic affiliate operations. The two cases in December prove this.
“NIS2 solves the problem.” NIS2 is necessary. Fundamental, even. But it's not enough. No regulation replaces operational capacity. NIS2 requires things to be done. It doesn't guarantee they will be done well. The difference between having a backup and having an offline, immutable, and monthly tested backup is the difference between recovering in hours and closing the doors. NIS2 says “business continuity.” LockBit 5.0 deletes shadow copies, kills backup services, and encrypts in minutes. These two realities coexist, and it is in the space between them that organizations are destroyed.
“This is just another ransomware cycle.” Cycles exist, it’s true. But each cycle brings more sophistication, more automation, and more resilience on the attacker’s side. LockBit survived an international police operation that dismantled its infrastructure. It returned with faster encryption, more sophisticated EDR evasion, a modular architecture that allows each affiliate to customize the attack by target, and evidence of coordination with other groups. Calling this “just another cycle” is like saying a Category 5 hurricane is “just another storm.” The scale and destructive capacity are not comparable.
What remains
The arrival of LockBit 5.0 in Portugal at Christmas 2025 is not just another ransomware incident. It is concrete proof that the country has entered the front line of cyber warfare. And that NIS2 has ceased to be a regulatory exercise and has become an operational urgency.
The question is no longer whether Portuguese organizations will be attacked. It is whether, when they are, they have the capacity to detect in minutes, contain in hours, and recover in days. It is whether the continuity plan that is in the drawer works at 11 pm on a Saturday. It is whether those who lead the organization understand that cybersecurity is not a line item in the IT budget, but a condition for the survival of the business.
NIS2 gives us the framework. LockBit 5.0 gives us the urgency. What we do with both defines whether Portugal is a country that reacts or a country that prepares.
April 2026 is here. LockBit 5.0 is already here.
Article also published in TeK Notícias media outlet:
***
About the author
Lucas Valente Lima is an Offensive Security Engineer at Highdome (Agap2IT), with over 10 years of experience in IT and 6+ years in cybersecurity. He is an OSCP, OSWP, eWPTX, CEH, CWES, and CPTS certified professional and conducts penetration testing on web applications, APIs, infrastructure, and networks. Founder of the Highdome Cybersecurity Academy and the “From Zero to Cyber Hero” program, he actively contributes to the cybersecurity community in Portugal.
References and Sources
[2] Hiscox Group. Hiscox Cyber Preparedness Report 2025.
[6] Trend Micro & UK National Crime Agency (NCA). Report on new developments at LockBit.
[7] Trellix Advanced Research Center. Analysis of data from the leaked LockBit administration panel.
[9] European Commission. Portugal — SME Fact Sheet 2025.
conteúdos relacionados
Interesting Content
Contenu intéressant
-404

.svg)










.svg)








